Role- and Attribute-Based Access Controls
The Gold Standard in RBAC and ABAC Software.
Guarantee least privilege and remove friction from managing access with Cakewalk's granular user groups.
Why RBAC and ABAC?
Stop Overprovisioning From Day One.
Give new employees the access they need to be productive—but only the access they need, based on least privilege.
Streamline Processes by Removing Ambiguity.
No more time-consuming access decisions and grey areas—birthright access via roles or attributes is clear-cut and keeps things logical.
Enhance Compliance and Audits.
RBAC and ABAC clearly define permissions, making audits and regulatory compliance easier by providing transparent visibility into who can access what.
Lay the Ground for Scalability.
RBAC and ABAC are the gold standard for implementing an identity governance process that remains highly effective as your company scales.
Who Benefits from RBAC and ABAC?
IT & Security Teams.
RBAC and ABAC guarantee least privilege and remove ambiguity from identity governance, streamlining processes.
Finance.
RBAC and ABAC are the most powerful way to stop overprovisioning from day one, reducing your attack surface and avoiding overspending.
Team Leads.
Reduced involvement in administrative tasks allows more focus on team performance.

HR Teams.
Birthright access removes friction from onboarding processes, guaranteeing compliance while enhancing the employee experience.
Employees.
RBAC and ABAC give new joiners the access they need, getting productive quickly—without annoying chasing of app owners.
How Do RBAC and ABAC Work?
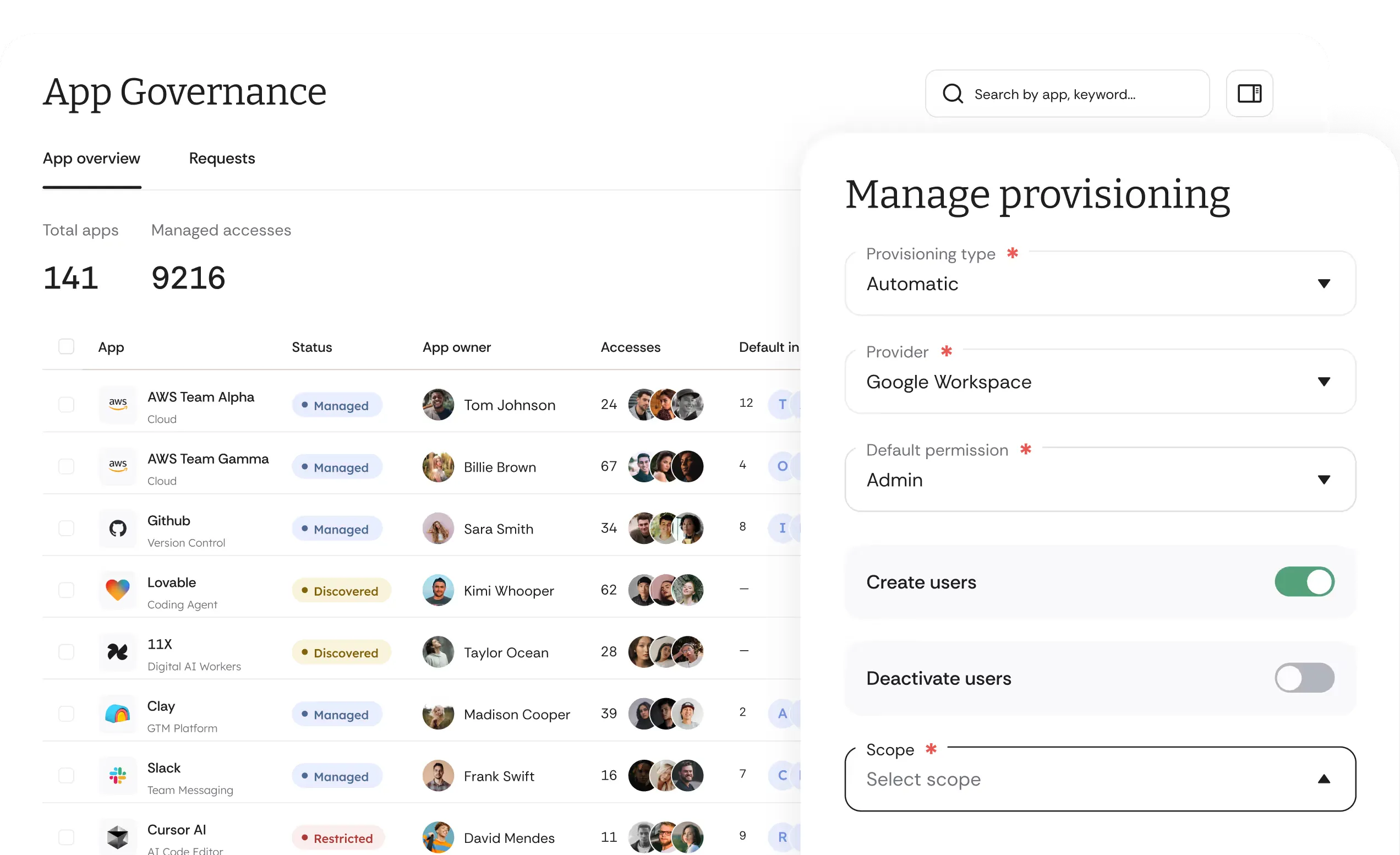
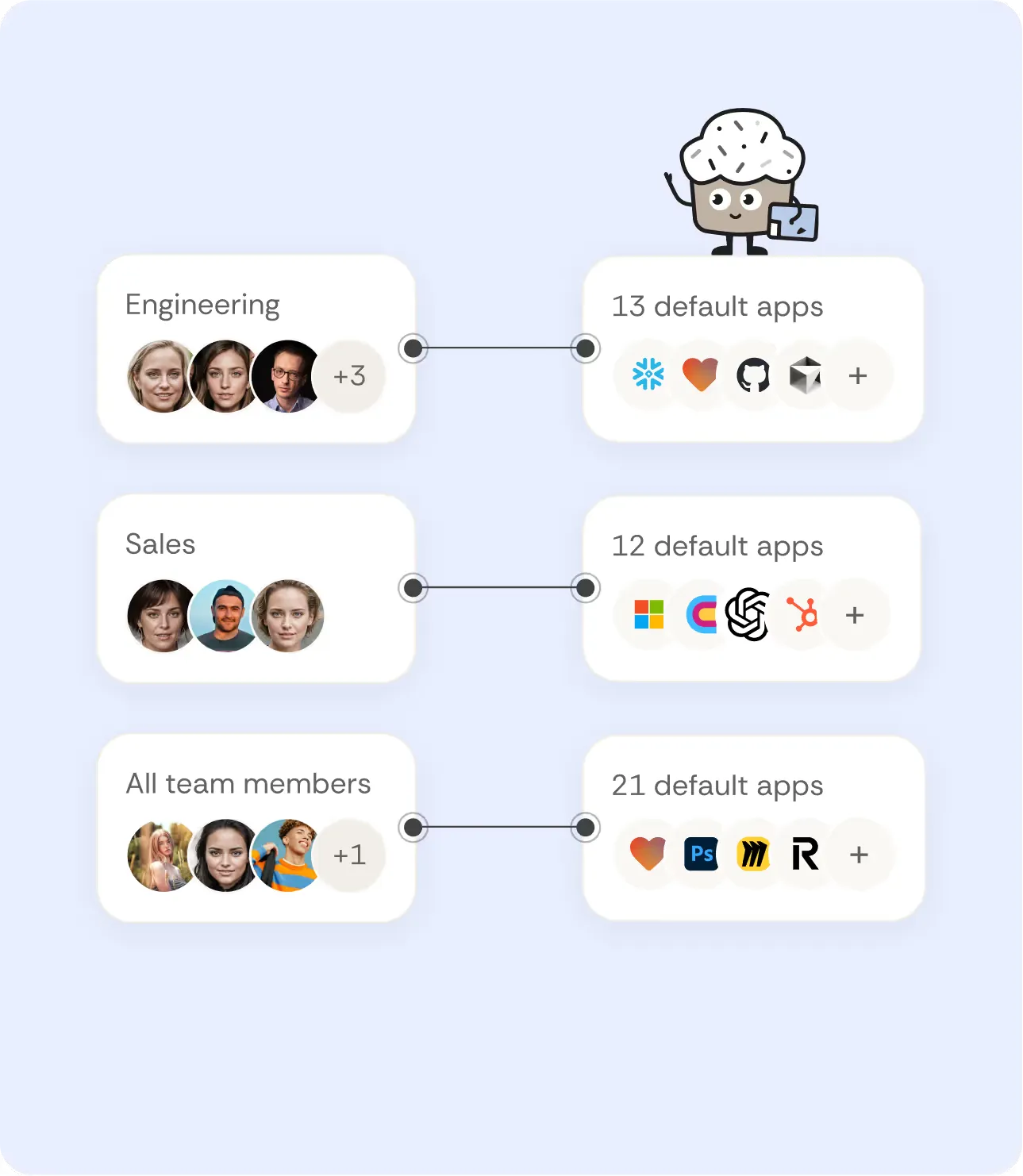
Sync and Set Up User Groups.
Import and sync user groups from your IdP, and define default access and restricted applications per group, based on roles or attributes.
Run RBAC or ABAC Onboarding.
Assign new users to user groups after they've been added to your IdP or HRIS, and trigger auto provisioning flows.
Learn more about Auto ProvisioningUse Groups to Manage JML.
Leverage groups to manage employees moving between departments and as a basis for offboarding when they leave your company.
Learn more about On/OffboardingEnterprise-Grade Access Management With Consumer-Grade Usability.
Deep Technical Power
Consolidate All Access Data
All identities, apps and AI agents. One system of record. Sync your key apps and agents in real time. Cut redundant tools by 25%.
Automate Workflows
Use Agent Cake to automate tedious access control processes.
Generate Insights
Get auto insights and take action based on clean access data.
Govern AI Agents
Gain visibility into the AI Agents your teams are using to guarantee fully compliant AI Governance.
Unlimited Customizations
Create workflows via our Policy Builder
Build your own approval workflows based on your specific organizational needs.
Customize views via our Smart Tables and Custom Fields.
Add individual meta context to every access via our Custom Fields and create your own dynamic views and reports in Smart Tables.
Differentiate between Managed and Non-Managed applications
For every app auto-detected by Cakewalk, decide whether the application is governed by your internal policies and Cakewalk or not.
Build with our Open API
Build custom workflows and integrations seamlessly using Cakewalk's Open API.
Intuitive User Experience
Get Going Easily
Get going with over 5,600 apps supported out-of-the-box, zero integration effort required.
Make IGA a Piece of Cake
Manage all IGA workflows in an intuitive, yet granular manner.
Enable your teams to comply
Get auto insights and take action based on clean access data.
RBAC and ABAC Are Just One Part of Cakewalk's Identity Governance Platform.
FAQs About RBAC and ABAC
Can I sync User Groups with my IdP?
Can I customize roles and permissions?
Do you "physically" block access to restricted applications?
How does RBAC improve security and compliance?